Cooperative Provable
Data Possession for Integrity Verification in Multi-Cloud Storage
ABSTRACT:
Provable data possession (PDP) is a
technique for ensuring the integrity of data in storage outsourcing. In this
paper, we address the construction of an efficient PDP scheme for distributed
cloud storage to support the scalability of service and data migration, in
which we consider the existence of multiple cloud service providers to
cooperatively store and maintain the clients’ data. We present a cooperative
PDP (CPDP) scheme based on homomorphic verifiable response and hash index
hierarchy. We prove the security of our scheme based on multi-prover
zero-knowledge proof system, which can satisfy completeness, knowledge
soundness, and zero-knowledge properties. In addition, we articulate
performance optimization mechanisms for our scheme, and in particular present
an efficient method for selecting optimal parameter values to minimize the
computation costs of clients and storage service providers. Our experiments
show that our solution introduces lower computation and communication overheads
in comparison with non-cooperative approaches.
ARCHITECTURE:
EXISTING SYSTEM
There exist various
tools and technologies for multicloud, such as Platform VM Orchestrator,
VMwarevSphere, and Ovirt. These tools help cloud providers construct a
distributed cloud storage platform for managing clients’ data. However, if such
an important platform is vulnerable to security attacks, it would bring
irretrievable losses to the clients. For example, the confidential data in an
enterprise may be illegally accessed through a remote interface provided by a
multi-cloud, or relevant data and archives may be lost or tampered with when
they are stored into an∙ uncertain storage pool outside the enterprise.
Therefore, it is indispensable for cloud service providers to provide security
techniques for managing their storage services.
PROPOSED SYSTEM
To check the availability and integrity of
outsourced data in cloud storages, researchers have proposed two basic
approaches called Provable Data Possession and Proofs of Retrievability
.Ateniese et al. first proposed the PDP model for ensuring possession of files
on untrusted storages and provided an RSA-based scheme for a static case that
achieves the communication cost. They also proposed a publicly verifiable
version, which allows anyone, not just the owner, to challenge the server for
data possession..They proposed a lightweight PDP scheme based on cryptographic
hash function and symmetric key encryption, but the servers can deceive the
owners by using previous metadata or responses due to the lack of randomness in
the challenges. The numbers of updates and challenges are limited and fixed in
advance and users cannot perform block insertions anywhere.
MODULES:
v Multi cloud storage
v Cooperative PDP
v Data Integrity
v Third Party Auditor
v Cloud User
MODULE DESCRIPTION:
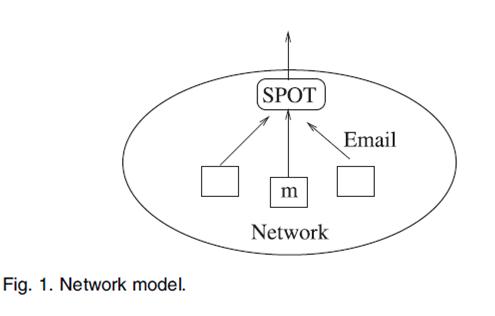
Multi
cloud storage
Distributed
computing is used to refer to any large collaboration in which many individual
personal computer owners allow some of their computer's processing time to be
put at the service of a large problem. In our system the each cloud admin
consist of data blocks. The cloud user uploads the data into multi cloud. cloud
computing environment is constructed based on open architectures and
interfaces, it has the capability to incorporate multiple internal and/or
external cloud services together to provide high interoperability. We call such
a distributed cloud environment as a multi-Cloud .A multi-cloud allows
clients to easily access his/her resources remotely through interfaces.
Cooperative
PDP
Cooperative PDP (CPDP) schemes adopting
zero-knowledge property and
three-layered index hierarchy, respectively. In particular efficient
method for selecting the optimal number of sectors in each block to minimize the
computation costs of clients and storage service providers. Cooperative PDP
(CPDP) scheme without compromising data privacy based on modern cryptographic
techniques
Data
Integrity
Data Integrity is very important in database
operations in particular and Data warehousing and Business intelligence in
general. Because Data Integrity ensured that data is of high quality, correct,
consistent and accessible.
Third Party Auditor
Trusted Third Party
(TTP) who is trusted to store verification parameters and offer public query
services for these parameters. In our system the Trusted Third Party, view the
user data blocks and uploaded to the distributed cloud. In distributed cloud
environment each cloud has user data blocks. If any Modification tried by cloud
owner an alert is send to the Trusted Third Party.
Cloud
User
The Cloud User who has a large amount of data
to be stored in multiple clouds and have the permissions to access and
manipulate stored data. The User’s Data is converted into data blocks. The data
blocks are uploaded to the cloud. The TPA views the data blocks and Uploaded in
multi cloud. The user can update the uploaded data. If the user wants to
download their files, the data’s in multi cloud is integrated and downloaded.
SYSTEM
REQUIREMENTS:
HARDWARE
REQUIREMENTS:
•
System : Pentium IV 2.4 GHz.
•
Hard
Disk : 40 GB.
•
Floppy
Drive : 1.44 Mb.
•
Monitor : 15 VGA Colour.
•
Mouse : Logitech.
•
Ram : 512 Mb.
SOFTWARE
REQUIREMENTS:
•
Operating system : - Windows XP.
•
Coding Language : J2EE
•
Data Base : MYSQL
REFERENCE:
Yan Zhu, Hongxin Hu, Gail-Joon Ahn,
Mengyang Yu, “Cooperative Provable Data Possession for Integrity Verification
in Multi-Cloud Storage”, IEEE
TRANSACTIONS ON PARALLEL AND DISTRIBUTED SYSTEMS.