Scalable and Secure
Sharing of Personal Health Records in Cloud Computing using Attribute-based
Encryption
CLICK HERE TO DOWNLOAD THE BASE PAPER
CLICK HERE TO DOWNLOAD THE BASE PAPER
Scalable and Secure
Sharing of Personal Health Records in Cloud Computing using Attribute-based
Encryption
ABSTRACT:
Personal health record (PHR) is an
emerging patient-centric model of health information exchange, which is often outsourced
to be stored at a third party, such as cloud providers. However, there have
been wide privacy concerns as personal health information could be exposed to
those third party servers and to unauthorized parties. To assure the patients’
control over access to their own PHRs, it is a promising method to encrypt the
PHRs before outsourcing. Yet, issues such as risks of privacy exposure, scalability
in key management, flexible access and efficient user revocation, have remained
the most important challenges toward achieving fine-grained, cryptographically
enforced data access control. In this paper, we propose a novel patient-centric
framework and a suite of mechanisms for data access control to PHRs stored in
semi-trusted servers. To achieve fine-grained and scalable data access control
for PHRs, we leverage attribute based encryption (ABE) techniques to encrypt
each patient’s PHR file. Different from previous works in secure data
outsourcing, we focus on the multiple data owner scenario, and divide the users
in the PHR system into multiple security domains that greatly reduces the key
management complexity for owners and users. A high degree of patient privacy is
guaranteed simultaneously by exploiting multi-authority ABE. Our scheme also
enables dynamic modification of access policies or file attributes, supports
efficient on-demand user/attribute revocation and break-glass access under
emergency scenarios. Extensive analytical and experimental results are
presented which show the security, scalability and efficiency of our proposed
scheme
ARCHITECTURE:
EXISTING SYSTEM:
Due to the high cost
of building and maintaining specialized data centers, many PHR services are
outsourced to or provided by third-party service providers, for example,
Microsoft Health Vault. While it is exciting to have convenient PHR services for
everyone, there are many security and privacy risks.
Which could
impede its wide adoption. The main concern is about whether the patients could
actually control the sharing of their sensitive personal health information (PHI),
especially when they are stored on a third-party server which people may not
fully trust.
DISADVANTAGES OF EXISTING SYSTEM:
There have been wide privacy concerns as
personal health information could be exposed to those third party servers and
to unauthorized parties.
Department of Veterans Affairs database
containing sensitive PHI of 26.5 million military veterans, including their
social security numbers and health problems was stolen by an employee who took
the data home without authorization.
They usually assume the use of a single
trusted authority (TA) in the system. This not only may create a load
bottleneck, but also suffers from the key escrow problem since the TA can
access all the encrypted files, opening the door for potential privacy exposure.
In addition, it is not practical to delegate all attribute management tasks to
one TA, including certifying all users’ attributes or roles and generating secret
keys.
PROPOSED SYSTEM:
To assure the patients’ control over
access to their own PHRs, it is a promising method to encrypt the PHRs before
outsourcing. In this paper, we propose a novel patient-centric framework and a
suite of mechanisms for data access control to PHRs stored in semi-trusted
servers. To achieve fine-grained and scalable data access control for PHRs, we
leverage attribute based encryption (ABE) techniques to encrypt each patient’s
PHR file.
To ensure patient-centric privacy
control over their own PHRs, it is essential to have fine-grained data access control
mechanisms that work with semi-trusted servers.
In order to protect the personal health
data stored on a semi-trusted server, we adopt attribute-based encryption (ABE)
as the main encryption primitive. Using ABE, access policies are expressed
based on the attributes of users or data, which enables a patient to
selectively share her PHR among a set of users by encrypting the file under a
set of attributes, without the need to know a complete list of users.
ADVANTAGES OF PROPOSED SYSTEM:
We focus on the multiple data owner
scenario, and divide the users in the PHR system into multiple security domains
that greatly reduces the key management complexity for owners and users.
In this paper, we bridge the above gaps
by proposing a unified security framework for patient-centric sharing of PHRs
in a multi-domain, multi-authority PHR system with many users. The framework
captures application level requirements of both public and personal use of a patient’s
PHRs, and distributes users’ trust to multiple authorities that better reflects
reality.
MODULES:
PHR Owner Module
Cloud Server Module
Attribute based Access Policy Module
Data confidentiality
Module
MODULE DESCRIPTION:
PHR Owner Module
The main goal of our framework is to
provide secure patient-centric PHR access and efficient key management at the
same time. The key idea is to divide the system into multiple security domains
(namely, public domains (PUDs) and personal domains (PSDs))
according to the different users’ data access requirements. The PUDs consist of
users who make access based on their professional roles, such as doctors,
nurses and medical researchers. In practice, a PUD can be mapped to an
independent sector in the society, such as the health care, government or insurance
sector. For each PSD, its users are personally associated with a data owner
(such as family members or close friends), and they make accesses to PHRs based
on access rights assigned by the owner.
Each data owner (e.g., patient) is a trusted
authority of her own PSD, who uses a KP-ABE system to manage the secret keys
and access rights of users in her PSD. Since the users are personally known by
the PHR owner, to realize patient-centric access, the owner is at the best position
to grant user access privileges on a case-by-case basis. For PSD, data
attributes are defined which refer to the intrinsic properties of the PHR
data, such as the category of a PHR file. For the purpose of PSD access, each
PHR file is labeled with its data attributes, while the key size is only linear
with the number of file categories a user can access. Since the number of users
in a PSD is often small, it reduces the burden for the owner. When encrypting
the data for PSD, all that the owner needs to know is the intrinsic data
properties.
Cloud
Server Module
In this paper, we consider the server to
be semi-trusted, i.e., honest but curious as those in [28] and [15]. That means
the server will try to find out as much secret information in the stored PHR
files as possible, but they will honestly follow the protocol in general. On
the other hand, some users will also try to access the files beyond their
privileges. For example, a pharmacy may want to obtain the prescriptions of
patients for marketing and boosting its profits. To do so, they may collude
with other users, or even with the server. In addition, we assume each party in
our system is preloaded with a public/private key pair, and entity
authentication can be done by traditional challenge-response protocols.
Attribute
based Access Policy Module
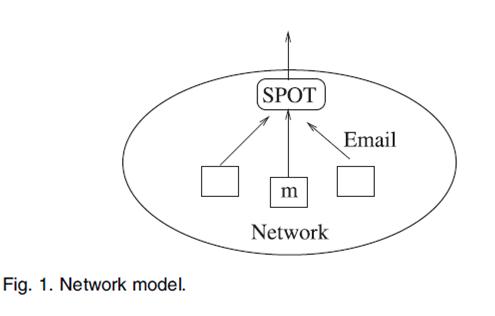
In our framework, there are multiple
SDs, multiple owners, multiple AAs, and multiple users. In addition, two ABE
systems are involved. We term the users having read and write access as data readers
and contributors, respectively.
Data confidentiality Module
The owners upload ABE-encrypted PHR
files to the server. Each owner’s PHR file is encrypted both under a certain
fine grained and role-based access policy for users from the PUD to access, and
under a selected set of data attributes that allows access from users in the
PSD. Only authorized users can decrypt the PHR files, excluding the server.
SYSTEM CONFIGURATION:-
HARDWARE REQUIREMENTS:-
ü Processor -Pentium –III
ü Speed - 1.1 Ghz
ü RAM - 256 MB(min)
ü Hard
Disk - 20 GB
ü Floppy
Drive - 1.44 MB
ü Key
Board - Standard Windows Keyboard
ü Mouse - Two or Three Button Mouse
ü Monitor - SVGA
SOFTWARE REQUIREMENTS:-
v Operating System : Windows95/98/2000/XP
v Application Server :
Tomcat5.0/6.X
v Front End : Java, JSP
v Script :
JavaScript.
v Server side Script : Java Server Pages.
v Database : MYSQL
REFERENCE:
Ming Li, Shucheng Yu, Yao Zheng,
Kui Ren, and Wenjing Lou, “Scalable and Secure Sharing of Personal
Health Records in Cloud Computing using Attribute-based Encryption” IEEE TRANSACTIONS ON PARALLEL AND
DISTRIBUTED SYSTEMS VOL. XX, NO. XX, XX 2012.
Scalable and Secure Sharing of Personal Health Records in Cloud Computing using Attribute-based Encryption, Scalable and Secure Sharing of Personal Health Records in Cloud Computing using Attribute-based Encryption 2012 ieee project, Scalable and Secure Sharing of Personal Health Records in Cloud Computing using Attribute-based Encryption java project, Scalable and Secure Sharing of Personal Health Records in Cloud Computing using Attribute-based Encryption doc, Scalable and Secure Sharing of Personal Health Records in Cloud Computing using Attribute-based Encryption ppt, Scalable and Secure Sharing of Personal Health Records in Cloud Computing using Attribute-based Encryption base paper, Scalable and Secure Sharing of Personal Health Records in Cloud Computing using Attribute-based Encryption review document, Scalable and Secure Sharing of Personal Health Records in Cloud Computing using Attribute-based Encryption source code, Scalable and Secure Sharing of Personal Health Records in Cloud Computing using Attribute-based Encryption ready made project, Scalable and Secure Sharing of Personal Health Records in Cloud Computing using Attribute-based Encryption with source code, Scalable and Secure Sharing of Personal Health Records in Cloud Computing using Attribute-based Encryption pondicherry, Scalable and Secure Sharing of Personal Health Records in Cloud Computing using Attribute-based Encryption details, 2012 ieee projects, 2012 ieee java projects, 2012 ieee
dotnet projects, 2012 ieee android projects, 2012 ieee matlab projects, 2012
ieee embedded projects, 2012 ieee robotics projects, 2012 IEEE EEE PROJECTS, 2012
IEEE POWER ELECTRONICS PROJECTS, ieee 2012 android projects, ieee 2012 java
projects, ieee 2012 dotnet projects, 2012 ieee mtech projects, 2012 ieee btech
projects, 2012 ieee be projects, ieee 2012 projects for cse, 2012 ieee cse
projects, 2012 ieee it projects, 2012 ieee ece projects, 2012 ieee mca
projects, 2012 ieee mphil projects, pondicherry ieee projects, best project
centre in pondicherry, bulk ieee projects, jpinfotech ieee projects, jp
infotech pondicherry, latest ieee projects, ieee projects for mtech, ieee
projects for btech, ieee projects for mphil, ieee projects for be, ieee
projects, student projects, students ieee projects, ieee proejcts india, ms
projects, bits pilani ms projects, uk ms projects, ms ieee projects, ieee
android real time projects, 2012 mtech projects, 2012 mphil projects, 2012 ieee
projects with source code, pondicherry mtech projects, jpinfotech ieee
projects, ieee projects, 2012 ieee project source code, journal paper
publication guidance, conference paper publication guidance, ieee project, free
ieee project, ieee projects for students., 2012 ieee omnet++ projects, ieee
2012 oment++ project, innovative ieee projects, latest ieee projects, 2012
latest ieee projects, ieee cloud computing projects, 2012 ieee cloud computing
projects, 2012 ieee networking projects, ieee networking projects, 2012 ieee
data mining projects, ieee data mining projects, 2012 ieee network security
projects, ieee network security projects, 2012 ieee image processing projects,
ieee image processing projects, ieee parallel and distributed system projects,
ieee information security projects, 2012 wireless networking projects ieee,
2012 ieee web service projects, 2012 ieee soa projects, ieee 2012 vlsi projects