Discovery and
Verification of Neighbor Positions in Mobile Ad Hoc Networks
ABSTRACT:
A growing number of ad hoc networking protocols and
location-aware services require that mobile nodes learn the position of their
neighbors. However, such a process can be easily abused or disrupted by
adversarial nodes. In absence of a priori trusted nodes, the discovery and
verification of neighbor positions presents challenges that have been scarcely
investigated in the literature. In this paper, we address this open issue by
proposing a fully distributed cooperative solution that is robust against
independent and colluding adversaries, and can be impaired only by an
overwhelming presence of adversaries. Results show that our protocol can thwart
more than 99 percent of the attacks under the best possible conditions for the
adversaries, with minimal false positive rates.
EXISTING SYSTEM:
Geographic routing in spontaneous networks, data gathering
in sensor networks, movement coordination among autonomous robotic nodes, location-specific
services for handheld devices, and danger warning or traffic monitoring in
vehicular networks are all examples of services that build on the availability
of neighbor position information. The correctness of node locations is
therefore an all important issue in mobile networks, and it becomes particularly
challenging in the presence of adversaries aiming at harming the system
DISADVANTAGES
OF EXISTING SYSTEM:
Ø Correctly
establish their location in spite of attacks feeding false location
information, and
Ø Verify
the positions of their neighbors, so as to detect adversarial nodes announcing
false locations.
PROPOSED SYSTEM:
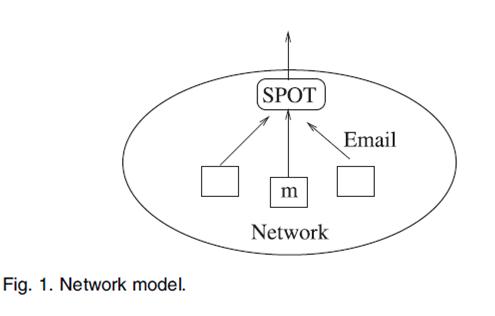
In this paper, we focus on the latter aspect,
hereinafter referred to as neighbor position verification (NPV for short). Specifically,
we deal with a mobile ad hoc network, where a pervasive infrastructure is not
present, and the location data must be obtained through node-to-node
communication. Such a scenario is of particular interest since it leaves the door
open for adversarial nodes to misuse or disrupt the location-based services.
For example, by advertising forged positions, adversaries could bias geographic
routing or data gathering processes, attracting network traffic and then eavesdropping
or discarding it. Similarly, counterfeit positions could grant adversaries
unauthorized access to location-dependent services, let vehicles forfeit road
tolls, disrupt vehicular traffic or endanger passengers and drivers.
ADVANTAGES
OF PROPOSED SYSTEM:
Ø Our
NPV scheme is compatible with state-of the-art security architectures,
including the ones that have been proposed for vehicular networks.
Ø It
is lightweight, as it generates low overhead traffic.
Ø It
is robust against independent and colluding adversaries
Ø It
leverages cooperation but allows a node to perform all verification procedures
autonomously
SYSTEM CONFIGURATION:-
HARDWARE REQUIREMENTS:-
ü Processor - Pentium –IV
ü Speed - 1.1 Ghz
ü RAM - 512 MB(min)
ü Hard
Disk - 40 GB
ü Key
Board - Standard Windows Keyboard
ü Mouse - Two or Three Button Mouse
ü Monitor - LCD/LED
SOFTWARE REQUIREMENTS:-
v Operating
System : LINUX
v Tool : Network
Simulator-2
v Front
End : OTCL (Object
Oriented Tool Command Language)
REFERENCE:
Marco Fiore,Member, IEEE, Claudio Ettore Casetti,
Member, IEEE, Carla-Fabiana Chiasserini,Senior Member, IEEE, and Panagiotis
Papadimitratos, Member, IEEE “Discovery and Verification of Neighbor Positions
in Mobile Ad Hoc Networks” - IEEE
TRANSACTIONS ON MOBILE COMPUTING, VOL. 12, NO. 2, FEBRUARY 2013.