2011- 2012 IEEE Java Project Titles
Online Intrusion Alert Aggregation with Generative Data Stream Modeling.
Embedded Extended Visual Cryptography Schemes
Architecting a Secure Enterprise Data Sharing Environment to the Edge
Robust Video Data Hiding Using Forbidden Zone Data Hiding and Selective Embedding
A Competitive Study of Cryptography Techniques over Block Cipher.
Analysis on Credit Card Fraud Detection Methods.
Text Clustering with Seeds Affinity Propagation
Clustering with Multi-Viewpoint based Similarity Measure.
On Demand Check Pointing for Grid Application Reliability using Communicating Process Model
Computational Perceptual Features for Texture Representation and Retrieval
Subspace-Based Striping Noise Reduction in Hyper-spectral Images
Ontology Based Business Process Customization for Composite Web Services
Design of p-Cycles for full node protection in WDM Mesh Networks
Dynamics of Malware Spread in Decentralized Peer-to-Peer Networks
Intrusion detection: An Energy efficient approach in Heterogeneous WSN
Dynamic Channel Allocation for Wireless Zone-Based Multicast and Broadcast Service
A Foundation for Stochastic Bandwidth Estimation of Networks with Random Service
Analysis of Quality of Object Oriented Systems using Object Oriented Metrics
A new approach for FEC decoding based on the BP algorithm in LTE and Wi-MAX systems
Simplified algorithm on network shortest path problem
Voronoi-based continuous query processing for mobile users
Geographical Routing With Location Service in Intermittently Connected MANETs
Resource Management Using Dynamical Load Prediction and Multiprocessor Cooperation
Minimizing Additive Distortion in Steganography Using Syndrome-Trellis Codes
Multiple exposure fusion for high dynamic range image acquisition
On the Information Flow Required for Tracking Control in Networks of Mobile Sensing Agents
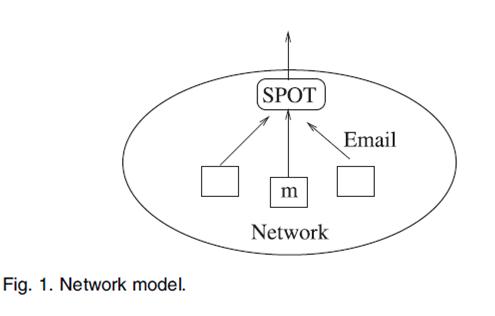
Selective Data Stream Blocking Mechanism for Networks
Mobile Sampling of Sensor Field Data Using Controlled Broadcast
Denial of Service Attacks in Wireless Networks: The Case of Jammers
Secure Communications Over Wireless Broadcast Networks: Stability and Utility Maximization
A Unified Approach to Optimizing Performance in Networks Serving Heterogeneous Flows
Load Shedding in Mobile Systems with MobiQual
Optimal Bandwidth Assignment for Multiple-Description-Coded Video
Coding for Cryptographic Security Enhancement Using Stopping Sets
Caching Strategies Based on Information Density
Enabling Public Auditability and Data Dynamics for Storage Security in Cloud Computing
Effective Navigation of Query Results Based on Concept Hierarchies
Nymble- Blocking Misbehaving Users in Anonymizing Networks
Modeling and Detection of Camouflaging Worm
Buffer Sizing for 802.11 Based Networks
SAT: A Security Architecture Achieving Anonymity and Traceability in Wireless Mesh Networks
Discovering Conditional Functional Dependencies
Ranking Spatial Data by Quality Preferences
Extended XML Tree Pattern Matching: Theories and Algorithms
Cloud Computing for Agent-Based Urban Transportation Systems
Secure and Practical Outsourcing of Linear Programming in Cloud Computing
Delay Analysis and Optimality of Scheduling Policies for Multi-Hop Wireless Networks
ProgME: Towards Programmable Network Measurement
Supporting Efficient and Scalable Multicasting over Mobile Ad Hoc Networks
A Privacy-Preserving Location Monitoring System for Wireless Sensor Networks
Selfish Overlay Network Creation and Maintenance
A Machine Learning Approach for Identifying Disease-Treatment Relations in Short Texts
Decision Trees for Uncertain Data
Secret-Fragment-Visible Mosaic Image–A New Computer Art and Its Application to Information Hiding
Locating Equivalent Servants over P2P Networks
Parametric Methods for Anomaly Detection in Aggregate Traffic